Phoenix the Tesla Has a Message for Car Makers
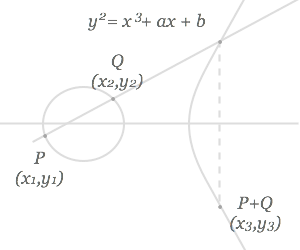
I could weep with joy. I’m finally home. Even though I kept myself busy tweeting my thoughts on Twitter, reading about the Kimye vs. Taylor Swift feud, and starting to work on my advanced mathematics degree, I am so happy to be home. …